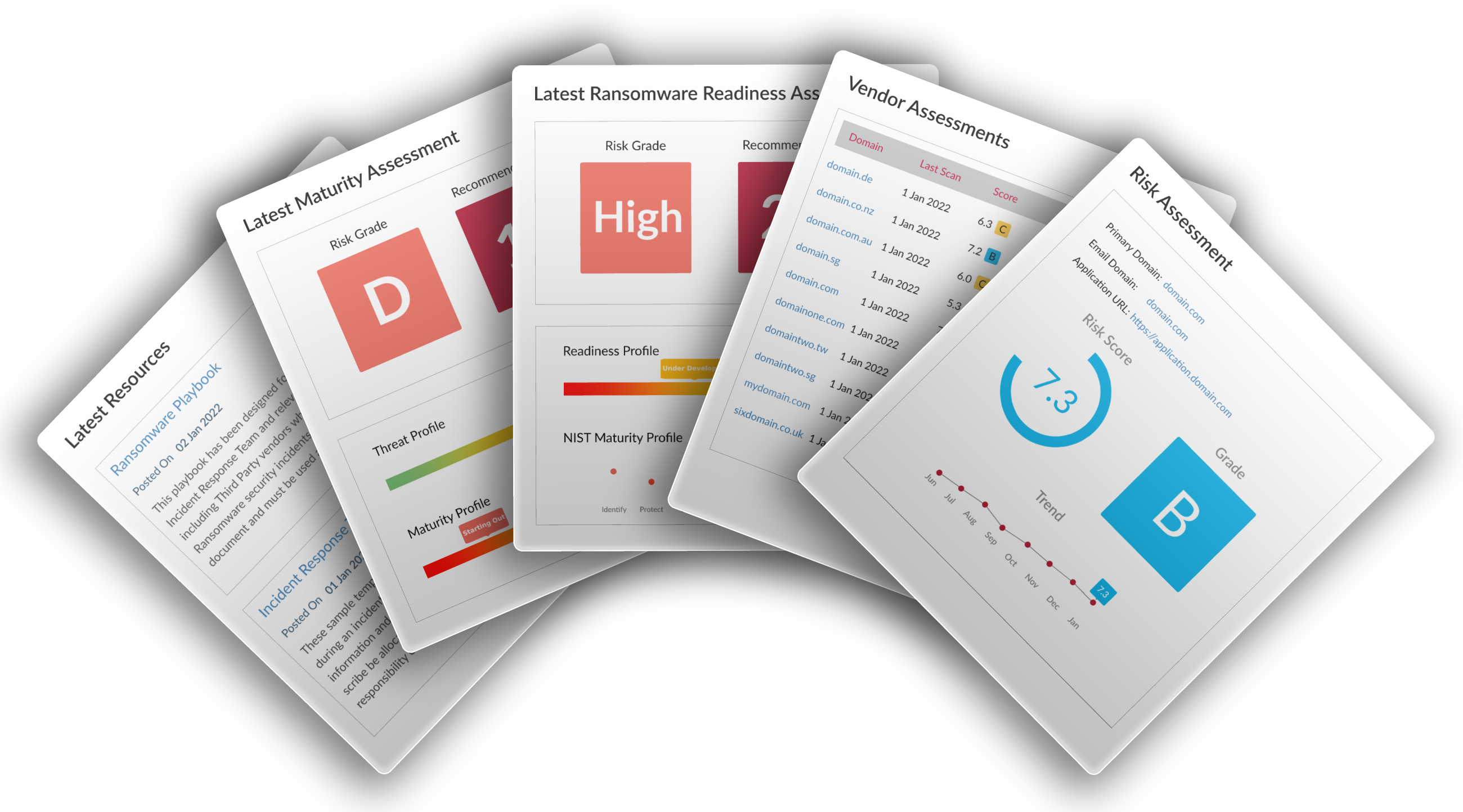
Vendor Risk
A Broad Risk Assessment
Security Colony uses a range of free, open source and commercial tools to complete over 20 distinct checks against a company’s online footprint, packaging this analysis in an easy to use interface detailing the identified risks and providing an overall risk score and grade for the assessed organization.
-
Assessing the organisation for historic (or current) malicious activity.
-
Assessing security misconfigurations and vulnerabilities related to server configuration.
-
Assessing security misconfigurations and vulnerabilities related to e-mail system configuration.
-
Assessing security misconfigurations and vulnerabilities related to critical web applications.
-
Details of email addresses easily discovered on the broader internet, leading to possible phishing attacks against the organization.
-
Discoverable subdomains listings, so you can ensure that nothing sensitive is being exposed.
-
Physical location map of all identified subdomain servers, based on the geo-location information.
-
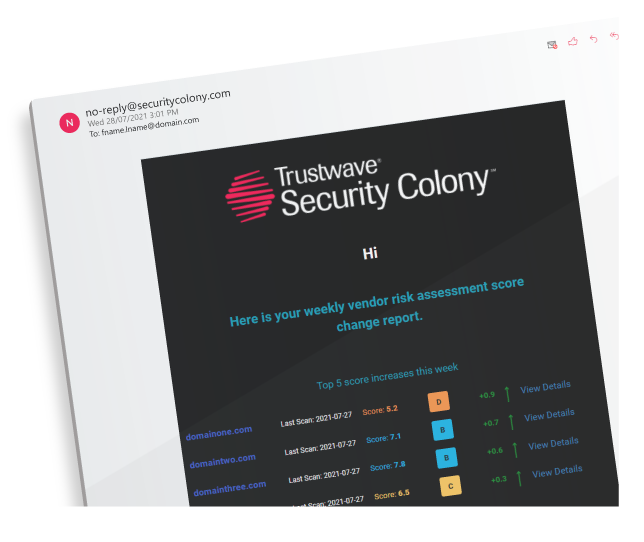
Receive vendor risk weekly or monthly score movement summaries by email.